Security Hardening in ProxySQL 3.0.7
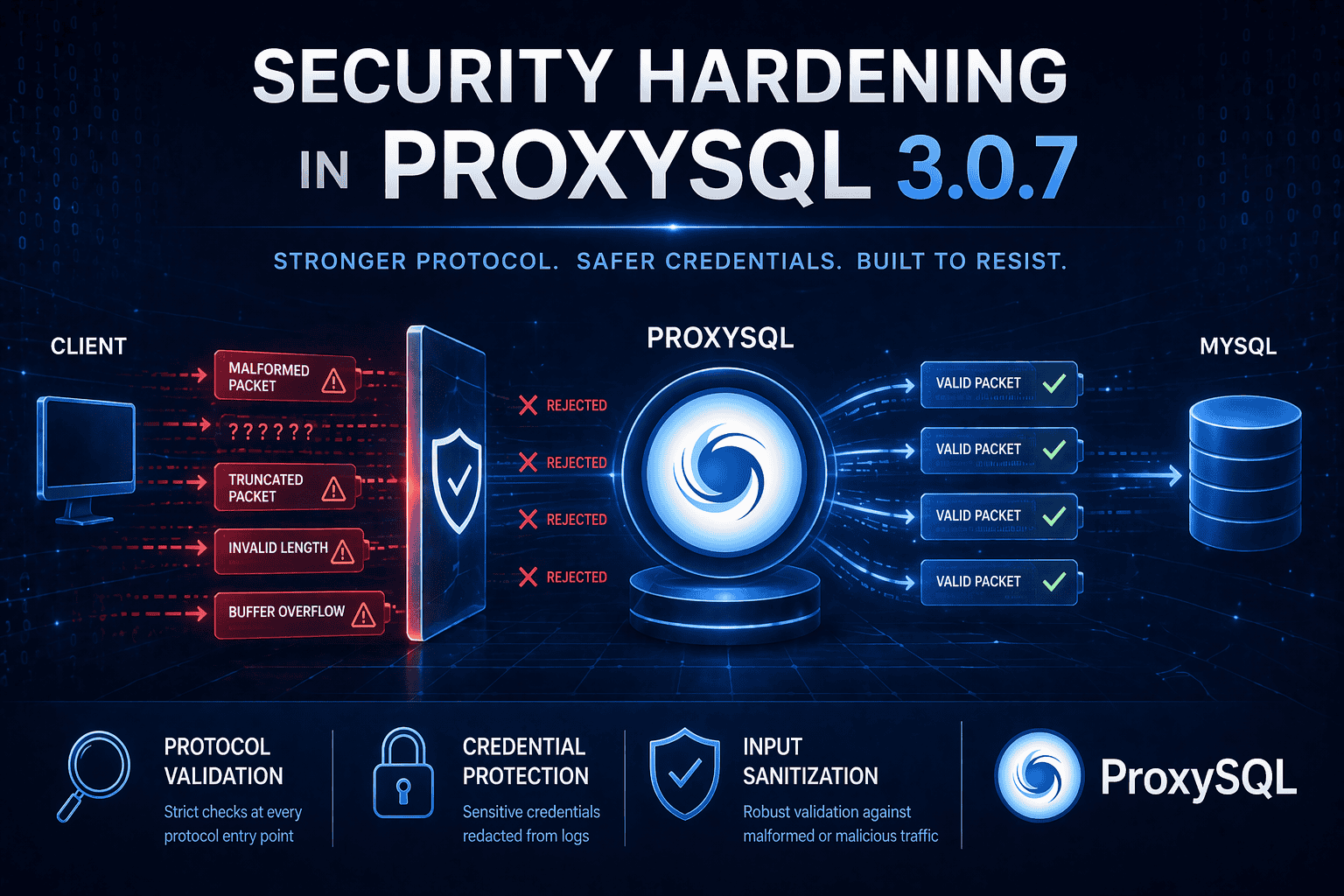
Security is a continuous process, not a one-time event. In ProxySQL 3.0.7 we applied systematic hardening across the MySQL protocol handler, the administrative interface, and the build toolchain. This post walks through each area and explains what changed and why.
Protocol Hardening
ProxySQL sits between clients and backend database servers, parsing and forwarding the MySQL wire protocol in real time. A malformed or truncated packet from a misbehaving client or a network error should never crash the proxy. With 3.0.7 we added explicit validation at multiple protocol entry points.
COM_BINLOG_DUMP
COM_BINLOG_DUMP is used by replica servers and binlog readers to request a binary log stream. A bug in the connection handler meant that if this command arrived while backends from a different hostgroup were idle, ProxySQL would dereference a null pointer and crash. In multi-hostgroup deployments with mixed workloads (read/write splitting alongside binlog routing), this was a real risk.
The fix validates the backend state before processing the command. If no suitable backend is found for the current session’s hostgroup, the command is rejected with a clean error instead of causing a segmentation fault.
COM_CHANGE_USER
COM_CHANGE_USER allows a client to re-authenticate on an existing connection. The handler reads user, database, and authentication data from the packet. Before 3.0.7, a packet shorter than the expected minimum length could cause out-of-bounds memory reads.
We added explicit bounds checking that validates minimum packet length before attempting to parse any fields. Packets that are too short are now rejected with ER_UNKNOWN_COM_ERROR.
HandshakeResponse
During the MySQL handshake, the client sends a HandshakeResponse packet containing username, database, authentication response, and other capability flags. The string fields in this packet (username, auth response, database, client plugin name) are length-prefixed, but the handler previously trusted the stated lengths without verifying they fell within the actual packet boundaries.
ProxySQL 3.0.7 validates that all string field offsets and lengths fall within the received packet size. Packets with inconsistent lengths are rejected at the handshake stage.
PROXY Protocol v1
The PROXY protocol (used by load balancers to pass client connection information) has a text-based v1 format like:
PROXY TCP4 192.168.1.1 192.168.1.2 12345 3306\r\nA buffer overflow in the address parsing code could be triggered by a source or destination address field exceeding the internal buffer size. The parser now validates address field lengths before copying into fixed-size buffers.
COM_STMT_SEND_LONG_DATA
COM_STMT_SEND_LONG_DATA is used to send large parameter values in chunks for prepared statements. A packet shorter than the minimum expected length (which includes the statement ID and parameter number) could cause incorrect parameter routing to backend servers. The handler now enforces minimum packet length before processing.
Credential Protection
Administrative credentials are a high-value target. When operators execute SET admin-admin_credentials = 'user:pass' via the admin interface, ProxySQL logs this activity for audit purposes. Starting with 3.0.7, the actual credential values are redacted in log output, preventing sensitive authentication data from appearing in log files, syslog aggregators, or monitoring dashboards.
This applies to all sensitive SET commands. The log entry records that a credential change was made and which variable was modified, but the actual value is replaced with ***.
Dependency Security
The test infrastructure uses Python dependencies for test orchestration and CI workflows. Dependabot identified 48 security vulnerabilities across these dependencies. All 48 have been resolved by bumping to the latest secure versions. While these dependencies are not part of the ProxySQL runtime binary, maintaining a clean supply chain across the entire development pipeline is important.
Recommendations
We recommend upgrading to 3.0.7 as soon as feasible, particularly for deployments that:
- Use multiple hostgroups with mixed read/write and binlog routing
- Expose the MySQL port to untrusted networks
- Process connections through load balancers using the PROXY protocol
- Run automated audit logging on administrative commands
The full list of changes is available in the 3.0.7 release notes.